about : Upload
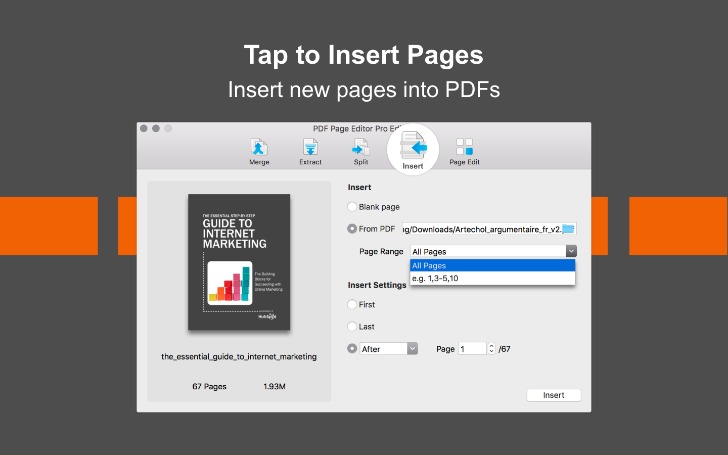
Drag and drop your PDF or image, or select it manually from your device via the dashboard. You can also connect to our API or document processing pipeline through Dropbox, Google Drive, Amazon S3, or Microsoft OneDrive.
Verify in Seconds
Our system instantly analyzes the document using advanced AI to detect fraud. It examines metadata, text structure, embedded signatures, and potential manipulation.
Get Results
Receive a detailed report on the document's authenticity—directly in the dashboard or via webhook. See exactly what was checked and why, with full transparency.
How automated systems analyze PDFs to detect forgeries
Automated detection systems combine a range of techniques to flag suspicious files. At the core of many solutions lies a layered analysis: file-level inspection, metadata extraction, structural parsing, and content validation. File-level inspection begins with checksums, file size anomalies, and format discrepancies; for example, a PDF that claims to be generated by a particular application but contains internal structures inconsistent with that application is often a red flag. Metadata extraction reads embedded fields like author, creation and modification dates, producer, and software identifiers. Discrepancies between claimed origins and embedded metadata often indicate tampering.

Structural parsing focuses on the PDF object model. PDFs are built from objects—streams, dictionaries, and cross-reference tables—and modern detectors parse these to identify unusual edits, orphaned objects, or mismatched cross-references that point to post-generation modification. Optical elements like embedded images and fonts are scanned for embedded watermarks or steganographic content. Content validation applies natural language processing and template matching: text anomalies, improbable font substitutions, inconsistent line spacing, and layout shifts can all betray manual edits or pasted content. Machine learning classifiers trained on labeled genuine and forged documents improve detection, learning patterns that humans might miss.
Signature verification is another crucial component. Digital signatures can be cryptographically validated against certificate chains, revealing whether a signature is valid, expired, revoked, or tampered with. Visual signatures, such as scanned signatures embedded as images, are analyzed for layering and re-use patterns. A robust system correlates signature validation with metadata and pixel-level analysis to reduce false positives. For organizations seeking a quick assessment, online services and integrated document pipelines make it easy to detect fake pdf instances and receive a transparent report showing which checks failed and why.
Practical manual techniques and visual indicators to spot fake PDFs
Even without specialized tools, several manual techniques reveal common forms of forgery. Begin by checking basic file properties: right-clicking the file to view properties or opening the PDF in a reader to inspect document information often exposes suspicious metadata. Compare the document's visible creation date with metadata timestamps—mismatches suggest subsequent edits. Zooming to high magnification can expose pasted text or images; jagged edges, inconsistent font rendering, or misaligned baselines indicate layer compositing rather than original typesetting. Inspecting fonts is particularly revealing: substitution of fonts causes spacing and kerning shifts that are obvious in side-by-side comparisons with known genuine documents.
Visual signatures and seals can be scrutinized for layering. Use a PDF viewer's layer or content panel to see if a signature image sits above or below text layers, or if multiple instances of the same signature appear across documents. Check for duplicated pixel patterns using simple image-editing tools; cloned signature segments are a hallmark of cut-and-paste fraud. Another manual checkpoint is hyperlinks and embedded objects: hover over links to see actual targets and examine attachments for mismatched filenames or unexpected file types. Many forgers neglect to sanitize hidden fields, comments, and annotations—revealing these can expose prior versions or notes indicating tampering.
Typography and spacing also offer clues. Official documents typically follow consistent templates, with fixed margins, tabulations, and pagination. Look for inconsistent line heights, uneven bullet alignment, or mixed bullet styles. Finally, cross-verify content against external sources: referenced identifiers, registration numbers, or official seals can often be confirmed through public registries. When uncertainty remains, combining manual inspection with a metadata-focused automated scan increases confidence in authenticity and highlights where deeper forensic analysis is warranted.
Case studies and real-world examples that illustrate fraud detection
Real-world incidents highlight the variety of tactics used to forge PDFs and how detection methods catch them. One common scenario involves forged invoices: a fraudster takes a legitimate invoice, edits payable details, and re-exports the file. Automated systems detect such tampering by identifying inconsistencies between the PDF’s internal creation timestamp and embedded image timestamps, or by spotting duplicated invoice numbers across files where no duplication should exist. In another case involving contractual documents, a document contained an embedded image of a signature that had been copied from an unrelated agreement. Forensic analysis revealed identical pixel clusters across two documents, proving reuse and casting doubt on the contract’s legitimacy.
Government forms and certificates are frequent targets. A notable example involved counterfeit academic diplomas where metadata showed the PDF was generated by consumer-level editing software rather than the institution’s standard publication tool. Cross-referencing digital signatures or institution-issued certificate serial numbers with public databases quickly exposed the forgery. In procurement fraud, manipulated bid documents often left behind hidden comments or annotations that referenced different bidders; these remnants were discovered by exposing hidden layers and revealed the document’s revision history, indicating collusion or fabrication.
These examples underline the importance of a combined approach: visual inspection, metadata analysis, and cryptographic checks. Organizations handling high-stakes documents should adopt a workflow that includes secure upload and processing, instantaneous automated scanning, and transparent reports showing what was verified and why. By integrating these steps into document handling pipelines, the risk of accepting a forged PDF as authentic is greatly reduced, protecting operations, finances, and reputations from sophisticated document fraud.