How fraudsters manipulate PDFs and the visual and technical signs to watch for
PDF-based fraud often begins with small, subtle manipulations that bypass casual inspection. Understanding common tampering methods makes it possible to detect fake pdf and to spot suspicious elements before financial or reputational damage occurs. Attackers typically alter text, replace images, or stitch multiple documents together to fabricate legitimacy. They may also modify metadata to disguise creation tools or timestamps, and they often use similar but not identical fonts and spacing to hide edits.
Visual cues are often the first line of defense. Look closely for inconsistent typefaces, irregular kerning or line spacing, mismatched margins, misaligned logos, and uneven image resolution. Scanned receipts and invoices may contain visual artifacts such as duplicated pixels, differing paper textures, or mismatched shadows when elements have been pasted in. Pay attention to numerical inconsistencies: totals that don’t add up, tax rates that are improbable for the jurisdiction, or invoice numbers that skip logical sequences.
Technical signs are equally important. File metadata can reveal the original application used to create the PDF, modification dates, and author fields; abrupt changes in these fields suggest post-creation edits. Embedded fonts or fonts replaced by system fallbacks can indicate that text was added after the original file was produced. Layered PDFs—where elements are placed on different layers—may hide edits on non-visible layers. Forensic examination of the PDF’s object streams and cross-reference tables can highlight anomalies such as duplicate object IDs or unusual compression patterns, which are common in tampered files. Combining visual and technical inspection significantly increases the ability to detect pdf fraud before acting on a document.
Tools, automated workflows, and best practices to detect fraud in PDF files
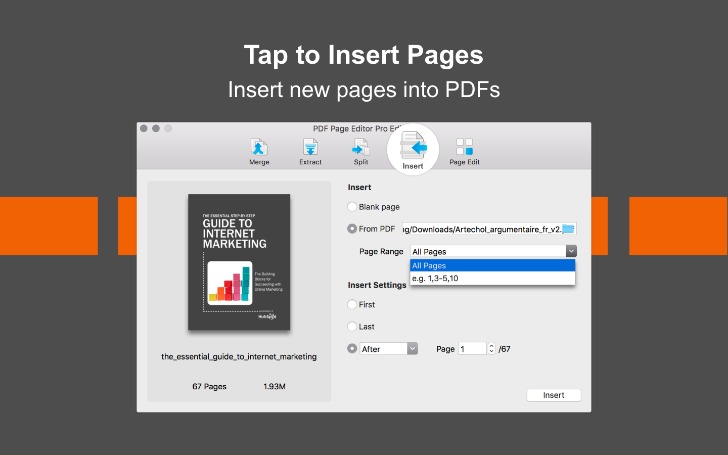
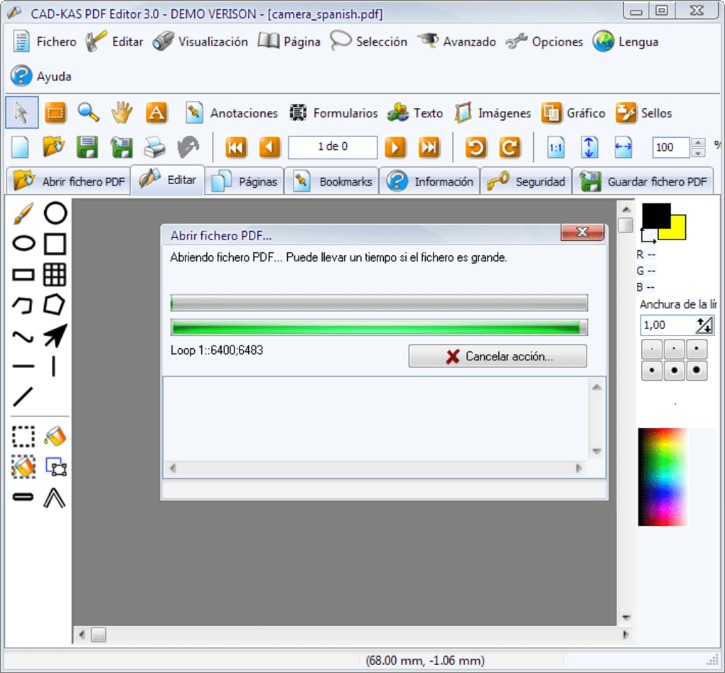
Deploying a combination of automated tools and manual checks creates a robust defense against document fraud. Start with a trusted PDF validation solution that checks signatures, verifies cryptographic hashes, and analyzes metadata. Digital signatures, when present and valid, provide a cryptographic guarantee of integrity; signature validation should be routine for invoices and contracts. Hash comparisons between a received PDF and the version stored in an internal system or provided by a supplier help quickly reveal modifications. Optical character recognition (OCR) tools convert scanned images into searchable text so that content-based searches and comparisons can spot inconsistencies across documents.
Automated anomaly detection tools can flag unexpected font substitutions, suspicious metadata edits, or embedded scripts. Malware and active-content scanning is necessary because some fraudulent PDFs contain macros or JavaScript designed to alter content or exfiltrate data. For teams that process many documents, building a workflow that includes document fingerprinting, automated checksum validation, and centralized logging makes it easier to trace back when a suspect document first appeared. Training staff on specific checks—verifying vendor bank details against a trusted ledger, confirming contact details via independent channels, and requiring purchase order matching—reduces the risk of falling for a convincing forgery.
For organizations seeking a fast verification step, online services streamline the process to detect fake invoice by combining signature checks, metadata analysis, and content verification. Integrating such verification steps into accounts payable and reimbursement procedures reduces manual workload while increasing the likelihood of catching forged documents early. Implementing two-factor verification for high-value payments—such as phone confirmation with a pre-registered contact—further mitigates risks that purely document-centric checks might miss.
Real-world case studies and practical measures to spot fake receipts and fraudulent invoices
Real cases illustrate how small oversights can lead to large losses. In one common scenario, attackers create fake vendor invoices that mirror legitimate invoices’ layout but direct funds to an alternate bank account. Detection often relies on cross-checking the beneficiary account against a known vendor profile and noticing subtle differences in the IBAN or routing number. In another frequent scheme, expense receipts are lightly edited—date ranges shifted, amounts rounded up, or merchant names swapped—to claim larger reimbursements. Expense management systems that enforce receipt-image matching and flag unusual patterns, such as repeated amounts or receipts submitted many times by the same user, can catch these schemes.
Case studies also highlight the value of metadata analysis. For example, a purportedly old contract showed a creation timestamp inconsistent with the document’s signed dates; further forensic review found that crucial pages had been inserted later. In travel reimbursement fraud, mismatches between boarding pass metadata and flight records exposed fabricated itineraries. These examples underline the importance of verifying PDF internals as well as visible content.
Practical measures include establishing clear verification steps: require invoice approval chains, maintain an internal registry of vendor bank details, and use automated tools to flag metadata inconsistencies. Encourage staff to check for visual red flags—blurry logos, uneven borders, or mismatched fonts—and to confirm unusual requests directly with known contacts. Keep an audit trail for every document processed, including checksum values and signature validation results, and perform periodic spot audits. For receipts and low-value items, random sampling with automated checks can deter casual fraud while preserving efficiency. Combining forensic checks, process controls, and employee awareness delivers a layered approach that improves the ability to detect fraud in pdf and prevents simple manipulations from causing significant harm.